It was 8 Could 1945, Victory in Europe Day. With the German navy’s unconditional give up, the European a part of World Struggle II got here to an finish. Alan Turing and his assistant Donald Bayley celebrated victory of their quiet English method, by taking a protracted stroll collectively. That they had been working aspect by aspect for greater than a 12 months in a secret electronics laboratory, deep within the English countryside. Bayley, a younger electrical engineer, knew little about his boss’s different life as a code breaker, solely that Turing would set off on his bicycle now and again to a different secret institution about 10 miles away alongside rural lanes, Bletchley Park. As Bayley and the remainder of the world would later study, Bletchley Park was the headquarters of an enormous, unprecedented code-breaking operation.
Once they sat down for a relaxation in a clearing within the woods, Bayley mentioned, “Effectively, the conflict’s over now—it’s peacetime, so you’ll be able to inform us all.”
Donald Bayley (1921-2020) graduated with a level in electrical engineering, and was commissioned into the Royal Electrical and Mechanical Engineers. There, he was chosen to work with Alan Turing on the Delilah undertaking. In later life he designed the teletypewriter-based “Piccolo” system for secret diplomatic radio communications, adopted by the British Overseas and Commonwealth Workplace and used worldwide for many years.Bonhams
“Don’t be so bloody foolish,” Turing replied.
“That was the tip of that dialog,” Bayley recalled 67 years later.
Turing’s unbelievable code-breaking work is now not secret. What’s extra, he’s famend each as a founding father of computer science and as a pioneering determine in artificial intelligence. He isn’t so well-known, nevertheless, for his work in electrical engineering. This can be about to alter.
In November 2023, a big cache of his wartime papers—nicknamed the “Bayley papers”—was
auctioned in London for nearly half one million U.S. {dollars}. The beforehand unknown cache comprises many sheets in Turing’s personal handwriting, telling of his top-secret “Delilah” engineering undertaking from 1943 to 1945. Delilah was Turing’s moveable voice-encryption system, named after the biblical deceiver of males. There may be additionally materials written by Bayley, usually within the type of notes he took whereas Turing was talking. It’s due to Bayley that the papers survived: He saved them till he died in 2020, 66 years after Turing handed away.
When the British Authorities realized concerning the sale of those papers at public sale, it acted swiftly to place a ban on their export, declaring them to be “an essential a part of our nationwide story,” and saying “It’s proper {that a} UK purchaser has the chance to buy these papers.” I used to be fortunate sufficient to get entry to the gathering previous to the November sale, when the public sale home requested for my help in figuring out a number of the technical materials. The Bayley papers shine new gentle on Turing the engineer.
On the time, Turing was touring from the summary to the concrete. The papers supply intriguing snapshots of his journey from his prewar deal with mathematical logic and quantity principle, into a brand new world of circuits, electronics, and engineering math.
Alan Turing’s Delilah Mission
Through the conflict, Turing realized that cryptology’s new frontier was going to be the encryption of speech. The present wartime cipher machines—such because the Japanese “
Purple” machine, the British Typex, and the Germans’ well-known Enigma and teletypewriter-based SZ42—have been all for encrypting typewritten textual content. Textual content, although, is scarcely essentially the most handy method for commanders to speak, and safe voice communication was on the navy want checklist.
Bell Labs’ pioneering
SIGSALY speech-encryption system was constructed in New York City, beneath a U.S. Military contract, throughout 1942 and 1943. It was gigantic, weighing over 50 thousand kilograms and filling a room. Turing was conversant in SIGSALY and wished to miniaturize speech encryption. The outcome, Delilah, consisted of three small items, every roughly the dimensions of a shoebox. Weighing simply 39 kg, together with its energy pack, Delilah can be at dwelling in a truck, a trench, or a big backpack.
 Bell Labs’ high secret set up of the SIGSALY voice-encryption system was a room-size machine that weighed over 50,000 kilograms.NSA
Bell Labs’ high secret set up of the SIGSALY voice-encryption system was a room-size machine that weighed over 50,000 kilograms.NSA
In 1943, Turing arrange bench house in a Nissen hut and labored on Delilah in secret. The hut was at Hanslope Park, a military-run institution in the course of nowhere, England. As we speak, Hanslope Park continues to be an ultrasecret intelligence website often called His Majesty’s Government Communications Centre. Within the Turing custom, HMGCC engineers provide at present’s British intelligence brokers with specialised {hardware} and software program.
Turing appears to have loved the 2 years he spent at Hanslope Park engaged on Delilah. He made an outdated cottage his dwelling and took meals within the Military mess. The commanding officer recalled that he “quickly settled down and have become certainly one of us.” In 1944, Turing acquired his younger assistant, Bayley, who had not too long ago graduated from the College of Birmingham with a bachelor’s diploma in electrical engineering. The 2 turned good pals, working collectively on Delilah till the autumn of 1945. Bayley known as Turing merely “Prof,” as everybody did within the Bletchley-Hanslope orbit.
“I admired the originality of his thoughts,” Bayley informed me once I interviewed him within the Nineteen Nineties. “He taught me an awesome deal, for which I’ve at all times been grateful.”
In return, Bayley taught Turing bench expertise. When he first arrived at Hanslope Park, Bayley discovered Turing wiring collectively circuits that resembled a “spider’s nest,” he mentioned. He took Turing firmly by the hand and dragged him by breadboarding boot camp.
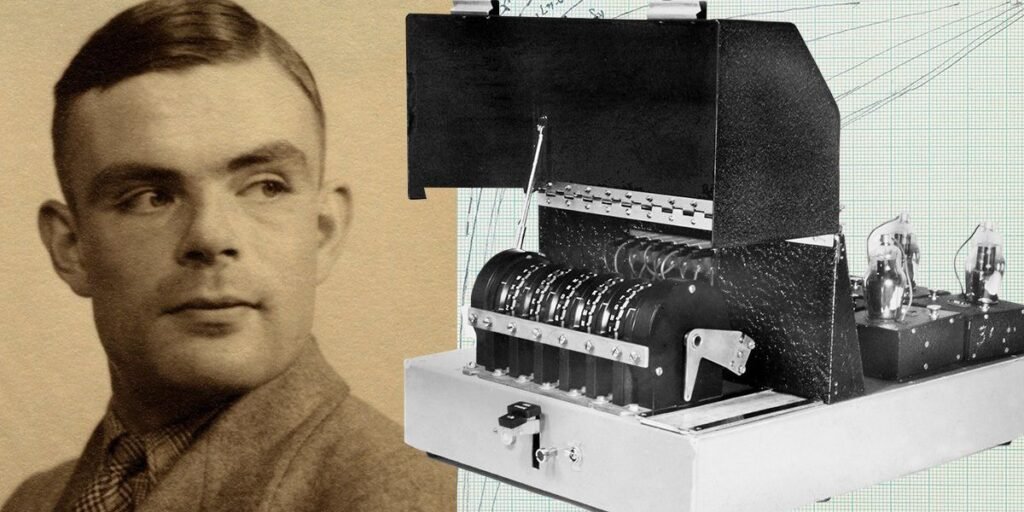
 Alan Turing and his assistant Donald Bayley created this working prototype of their voice-encryption system, known as Delilah.The Nationwide Archives, London
Alan Turing and his assistant Donald Bayley created this working prototype of their voice-encryption system, known as Delilah.The Nationwide Archives, London
A 12 months later, because the European conflict floor to an in depth, Turing and Bayley bought a prototype system up and operating. This “did all that could possibly be anticipated of it,” Bayley mentioned. He described the Delilah system as “one of many first to be primarily based on rigorous cryptographic rules.”
How Turing’s Voice-Encryption System Labored
Turing drew inspiration for the voice-encryption system from current cipher machines for textual content. Teletypewriter-based cipher machines such because the Germans’ subtle SZ42—damaged by Turing and his colleagues at Bletchley Park—labored otherwise from the higher identified Enigma machine. Enigma was normally used for messages transmitted over radio in Morse code. It encrypted the letters
A by Z by lighting up corresponding letters on a panel, known as the lampboard, whose electrical connections with the keyboard have been regularly altering. The SZ42, against this, was connected to an everyday teletypewriter that used a 5-bit telegraph code and will deal with not simply letters, but additionally numbers and a spread of punctuation. Morse code was not concerned. (This 5-bit telegraph code was a forerunner of ASCII and Unicode and continues to be utilized by some ham radio operators.)
The SZ42 encrypted the teletypewriter’s output by including a sequence of obscuring telegraph characters, known as key (the singular type “key” was utilized by the codebreakers and codemakers as a mass noun, like “footwear” or “output”), to the plain message. For instance, if the German plaintext was ANGREIFEN UM NUL NUL UHR (Assault at zero hundred hours), and the obscuring characters that have been getting used to encrypt these three phrases (and likewise the house between them) have been Y/RABV8WOUJL/H9VF3JX/D5Z, then the cipher machine would first add “Y” to “A”—that’s to say, add the 5-bit code of the primary letter of the important thing to the 5-bit code of the primary letter of the plaintext—after which added “/” to “N”, then “R” to “G”, and so forth. Below the SZ42’s guidelines for character addition (which have been hardwired into the machine), these 24 additions would produce PNTDOOLLHANC9OAND9NK9CK5, which was the encrypted message. This precept of producing the obscuring key after which including it to the plain message was the idea that Turing prolonged to the brand new territory of speech encryption.
 The Delilah voice-encryption machine contained a key unit that generated the pseudorandom numbers used to obscure messages. This blueprint of the important thing unit options 8 multivibrators (labeled “v1,” “v2,” and so forth).The Nationwide Archives, London
The Delilah voice-encryption machine contained a key unit that generated the pseudorandom numbers used to obscure messages. This blueprint of the important thing unit options 8 multivibrators (labeled “v1,” “v2,” and so forth).The Nationwide Archives, London
Contained in the SZ42, the important thing was produced by a key generator, consisting of a system of 12 wheels. Because the wheels turned, they churned out a continuing stream of seemingly random characters. The wheels within the receiver’s machine have been synchronized with the sender’s, and so produced the identical characters—Y/RABV8WOUJL/H9VF3JX/D5Z in our instance. The receiving machine subtracted the important thing from the incoming ciphertext PNTDOOLLHANC9OAND9NK9CK5, revealing the plaintext ANGREIFEN9UM9NUL9NUL9UHR (an area was at all times typed as “9”).
Making use of an identical precept, Delilah added the obscuring key to spoken phrases. In Delilah’s case, the important thing was a stream of pseudorandom numbers—that’s, random-seeming numbers that weren’t really random. Delilah’s key generator contained 5 rotating wheels and a few fancy electronics concocted by Turing. As with the SZ42, the receiver’s key generator needed to be synchronized with the sender’s, in order that each machines produced an identical key. Of their as soon as extremely secret however
now declassified report, Turing and Bayley commented that the issue of synchronizing the 2 key turbines had introduced them with “formidable difficulties.” However they overcame these and different issues, and finally demonstrated Delilah utilizing a recording of a speech given by Winston Churchill, efficiently encrypting, transmitting, and decrypting it.
 This loose-leaf sheet exhibits a circuit utilized by Turing in an experiment to measure the cut-off voltage at a triode tube, almost certainly in reference to the avalanche-effect fundamental to a multivibrator. Multivibrators have been an integral part of Delilah’s key-generation module. Bonhams
This loose-leaf sheet exhibits a circuit utilized by Turing in an experiment to measure the cut-off voltage at a triode tube, almost certainly in reference to the avalanche-effect fundamental to a multivibrator. Multivibrators have been an integral part of Delilah’s key-generation module. Bonhams
The encryption-decryption course of started with discretizing the audio sign, which at present we’d name analog-to-digital conversion. This produced a sequence of particular person numbers, every akin to the sign’s voltage at a specific cut-off date. Then numbers from Delilah’s key have been added to those numbers. Through the addition, any digits that wanted to be carried over to the following column have been ignored of the calculation—known as “noncarrying” addition, this helped scramble the message. The ensuing sequence of numbers was the encrypted type of the speech sign. This was transmitted routinely to a second Delilah on the receiving finish. The receiving Delilah subtracted the important thing from the incoming transmission, after which transformed the ensuing numbers to voltages to breed the unique speech.
The outcome was “whistly” and stuffed with background noise, however normally intelligible—though if issues went mistaken, there could possibly be “a sudden crack like a rifle shot,” Turing and Bayley reported cheerfully.
However the conflict was winding down, and the navy was not interested in the system. Work on the Delilah undertaking stopped not lengthy after the conflict ended, when Turing was employed by the British Nationwide Bodily Laboratory to design and develop an digital laptop. Delilah “had little potential for additional growth,” Bayley mentioned and “was quickly forgotten.” But it provided a really excessive degree of safety, and was the primary profitable demonstration of a compact moveable system for voice encryption.
What’s extra, Turing’s two years of immersion in electrical engineering stood him in good stead, as he moved on to designing digital computer systems.
Turing’s Lab Pocket book
The 2 years Turing spent on Delilah produced the Bayley papers. The papers comprise a laboratory pocket book, a substantial amount of unfastened sheets (some organized into bundles), and—the jewel of the gathering—a looseleaf ring binder bulging with pages.
The greenish-gray quarto-size lab pocket book, a lot of it in Turing’s handwriting, particulars months of labor. The primary experiment Turing recorded concerned measuring a pulse emitted by a
multivibrator, which is a circuit that may be triggered to supply a single voltage pulse or a sequence of pulses. Within the experiment, the heart beat was fed into an oscilloscope and its form examined. Multivibrators have been essential elements of Turing’s all-important key generator, and the following web page of the pocket book, labeled “Measurement of ‘Heaviside operate,’ ” exhibits the voltages measured in a part of the identical multivibrator circuit.
 A key merchandise within the Bayley papers is that this lab pocket book, whose first 24 pages are in Turing’s handwriting. These element Turing’s work on the Delilah undertaking previous to Bayley’s arrival in March 1944.Bonhams
A key merchandise within the Bayley papers is that this lab pocket book, whose first 24 pages are in Turing’s handwriting. These element Turing’s work on the Delilah undertaking previous to Bayley’s arrival in March 1944.Bonhams
As we speak, there’s intense curiosity in using multivibrators in cryptography. Turing’s key generator, essentially the most authentic a part of Delilah, contained eight multivibrator circuits, together with the five-wheel meeting talked about beforehand. In impact the multivibrators have been eight extra very sophisticated “wheels,” and there was extra circuitry for enhancing the random look of the numbers the multivibrators produced.
Subsequent experiments recorded within the lab e-book examined the efficiency of all the principle components of Delilah—the heart beat modulator, the harmonic analyzer, the important thing generator, the sign and oscillator circuits, and the radio frequency and aerial circuits. Turing labored alone for about the primary six months of the undertaking, earlier than Bayley’s arrival in March 1944, and the pocket book is in Turing’s handwriting as much as and together with the testing of the important thing generator. After this, the job of recording experiments handed to Bayley.
The Bandwidth Theorem
 Two unfastened pages, in Turing’s handwriting, clarify the so-called bandwidth theorem, now often called the Nyquist-Shannon sampling theorem. This was probably written out for Bayley’s profit. Bonhams
Two unfastened pages, in Turing’s handwriting, clarify the so-called bandwidth theorem, now often called the Nyquist-Shannon sampling theorem. This was probably written out for Bayley’s profit. Bonhams
Among the many piles of unfastened sheets coated with Turing’s riotously untidy handwriting, one web page is headed “Bandwidth Theorem.” Delilah was in impact an utility of a bandwidth theorem that at present is called the Nyquist-Shannon
sampling theorem. Turing’s proof of the concept is scrawled over two sheets. Most likely he wrote the proof out for Bayley’s profit. The theory—which expresses what the sampling price must be if sound waves are to be reproduced precisely—ruled Delilah’s conversion of sound waves into numbers, performed by sampling vocal frequencies a number of thousand instances a second.
At Bell Labs, Claude Shannon had written a paper sketching earlier work on the concept after which proving his personal formulation of it. Shannon wrote the paper in 1940, though it was not printed till 1949. Turing worked at Bell Labs for a time in 1943, in reference to SIGSALY, earlier than returning to England and embarking on Delilah. It appears probably that he and Shannon would have mentioned sampling charges.
Turing’s “Pink Kind” Notes
Through the conflict, Hanslope Park housed a big radio-monitoring part. Shifts of operators repeatedly searched the airwaves for enemy messages. Enigma transmissions, in Morse code, have been recognized by their stereotypical navy format, whereas the distinctive warble of the SZ42’s radioteletype indicators was immediately recognizable. After latching onto a transmission, an operator crammed out an Military-issue type (preprinted in shiny crimson ink). The frequency, the time of interception, and the letters of ciphertext have been famous down. This “crimson type” was then rushed to the code breakers at Bletchley Park.
 Writing paper was briefly provide in wartime Britain, and Turing used the clean reverse sides of those “crimson types,” designed for radio operators to notice down details about intercepted indicators.Bonhams
Writing paper was briefly provide in wartime Britain, and Turing used the clean reverse sides of those “crimson types,” designed for radio operators to notice down details about intercepted indicators.Bonhams
Writing paper was briefly provide in wartime Britain. Turing evidently helped himself to massive handfuls of crimson types, scrawling out screeds of notes about Delilah on the clean reverse sides. In a single bundle of crimson types, numbered by Turing on the corners, he thought of a resistance-capacitance community into which a “pulse of space A at time 0” is enter. He calculated the cost as the heart beat passes by the community, after which calculated the “output volts with pulse of that space.” The next sheets are coated with integral equations involving time, resistance, and cost. Then a scribbled diagram seems, by which a wavelike pulse is analyzed into discrete “steps”—a prelude to a number of pages of
Fourier-type evaluation. Turing appended a proof of what he termed the “Fourier theorem,” proof that these pages might have been a tutorial for Bayley.
The very look of those papers speaks to the character and difficult nature of the Delilah undertaking. The usually top-secret Military crimson types, the proof of wartime shortages, the scribbled formulation, the complexity of the mathematics, the tutorials for Bayley—all contribute to the image of the Prof and his younger assistant working carefully collectively at a secret navy institution on a tool that pushed the engineering envelope.
Turing’s Lectures for Electrical Engineers
The duvet of the looseleaf ring binder is embossed in gilt letters “Queen Mary’s Faculty, Walsall,” the place Bayley had as soon as been a pupil. It’s full of handwritten notes taken by Bayley throughout a sequence of night lectures that Turing gave at Hanslope Park. The dimensions of Turing’s viewers is unknown, however there have been quite a few younger engineers like Bayley at Hanslope.
These notes can moderately be given the title
Turing’s Lectures on Superior Arithmetic for Electrical Engineers. Working to 180 pages, they’re essentially the most intensive noncryptographic work by Turing at the moment identified, vying in size together with his 1940 write-up about Enigma and the Bombe, affectionately identified at Bletchley Park as “Prof’s E book.”
Stepping again slightly helps to place this essential discovery into context. The normal image of Turing held him to be a mathematician’s mathematician, dwelling in a realm far faraway from sensible engineering. In 1966, as an illustration,
Scientific American ran an article by the legendary laptop scientist and AI pioneer John McCarthy, by which he acknowledged that Turing’s work didn’t play “any direct position within the labors of the boys who made the pc a actuality.” It was a standard view on the time.
 A binder crammed with Bayley’s notes of Turing’s lectures is the jewel of the not too long ago offered doc assortment.Bonhams
A binder crammed with Bayley’s notes of Turing’s lectures is the jewel of the not too long ago offered doc assortment.Bonhams
As we now know, although, after the conflict Turing himself designed an digital laptop, known as the Automated Computing Engine, or ACE. What’s extra, he designed the programming system for the Manchester College “Child” laptop, in addition to the {hardware} for its punched-tape enter/output. Child got here to life in mid-1948. Though small, it was the primary really stored-program digital laptop. Two years later, the prototype of Turing’s ACE ran its first program. The prototype was later commercialized because the English Electrical DEUCE (Digital Digital Common Computing Engine). Dozens of DEUCEs have been bought—massive gross sales in these days—and so Turing’s laptop turned a serious workhorse in the course of the first a long time of the Digital Age.
But the picture has continued of Turing as somebody who made elementary but summary contributions, slightly than as somebody whose endeavors typically match onto the spectrum from bench electronics by to engineering principle. The Bayley papers carry a unique Turing into focus: Turing the artistic electrical engineer, with blobs of solder throughout his footwear—even when his soldered joints did tend to come back aside, as Bayley liked to narrate.
Turing’s lecture notes are in impact a textbook, terse and selective, on superior math for circuit engineers, though now very out-of-date, in fact.
There may be little particularly about electronics within the lectures, apart from passing mentions, resembling a reference to cathode followers. When speaking concerning the Delilah undertaking, Bayley preferred to say that Turing had solely not too long ago taught himself elementary electronics, by learning an RCA vacuum tube handbook whereas he crossed the Atlantic from New York to Liverpool in March 1943. This can’t be totally correct, nevertheless, as a result of in 1940 Turing’s “Prof’s E book” described using some electronics. He detailed an association of 26 thyratron tubes powered by a 26-phase provide, with every tube controlling a double-coil relay “which solely journeys if the thyratron fails to fireside.”
Turing’s data of sensible electronics was in all probability inferior to his assistant’s, initially anyway, since Bayley had studied the topic at college after which was concerned with radar earlier than his switch to Hanslope Park. When it got here to the mathematical aspect of issues, nevertheless, the state of affairs was very totally different. The Bayley papers reveal the maturity of Turing’s data of the arithmetic {of electrical} circuit design—data that was important to the success of the Delilah undertaking.
The weird breadth of Turing’s mental skills—mathematician, logician, code breaker, thinker, laptop theoretician, AI pioneer, and computational biologist—is already half and parcel of his public persona. To those should now even be added an appreciation of his idiosyncratic prowess in electrical engineering.
A number of the content material on this story initially appeared in Jack Copeland’s report for the Bonhams public sale home.
From Your Website Articles
Associated Articles Across the Internet